New Software Feature
Introducing Advanced Permissions

You’re the Chief Security Officer for an organization with 53 sites, and your company has just completed security assessments for all of them. Each report details the security vulnerabilities at every site — so it’s information you’d like to keep private.
You need to be able to see all the reports, but not everyone on your team should have the same level of access. Building managers only need access to their own site’s report. Regional managers should only have access to the sites in their territories. Assessors should only be able to see the reports they completed.
How can you make sure everyone has the appropriate level of access, especially if you’re assessing hundreds of sites?
Introducing Advanced Permissions
Not everyone in an organization needs the same level of access. According to InfoSecurity Magazine, 44% of organizations were found to have experienced a security breach in the last year. Of those companies, 74% said that the breach occurred because too much privileged access had been given to third parties who didn’t need that level of permission.
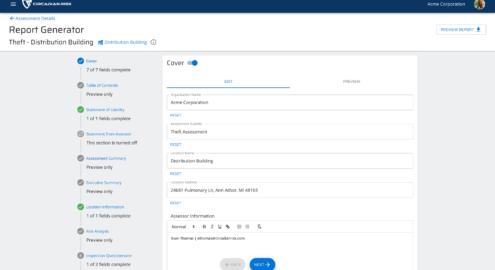
Circadian Risk’s Advanced Permissions feature lets you limit who can see certain information. We can restrict permission in two ways:
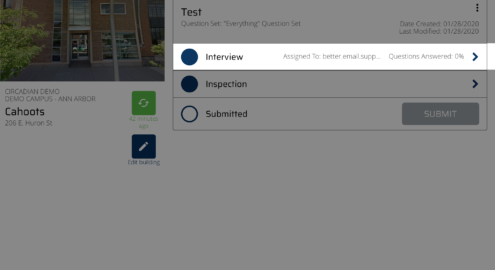
- By location: This lets only the personnel affiliated with any layer such as a building or level. For example a site manager will only see the assessments for that site.
- By individual assessment: If you’re using third party or security officers as assessors, this feature allows you to restrict access by the assessments themselves.
Permissions will also be applied to features like corrective action plans, so that tasks can be assigned to specific individuals or group of individuals without revealing every vulnerability to all your employees. For example, the janitor assigned to change a light bulb doesn't need access to information about your cyber vulnerabilities. The last thing you need is a comment on an assessment from someone who is in an irrelevant department.
But what’s more secure than traditional paper assessments?
A lot, to be honest. Traditional assessments, like Word documents, spreadsheets and paper reports aren’t secure at all — anyone can find and read them. Notes on a piece of paper or a pad aren’t secure either, unless your assessors are conscientiously shredding their notes. Emailing reports is also not secure.
When you use a tool like Circadian Risk, however, your notes are on a secure device, stored behind an encrypted portal, and assigned to only the people who need to see them.
Want to learn more? Contact us now for a demo.